Related Research Articles

An advance-fee scam is a form of fraud and is one of the most common types of confidence tricks. The scam typically involves promising the victim a significant share of a large sum of money, in return for a small up-front payment, which the fraudster claims will be used to obtain the large sum. If a victim makes the payment, the fraudster either invents a series of further fees for the victim to pay or simply disappears.

Phishing is a form of social engineering and scam where attackers deceive people into revealing sensitive information or installing malware such as ransomware. Phishing attacks have become increasingly sophisticated and often transparently mirror the site being targeted, allowing the attacker to observe everything while the victim is navigating the site, and transverse any additional security boundaries with the victim. As of 2020, it is the most common type of cybercrime, with the FBI's Internet Crime Complaint Center reporting more incidents of phishing than any other type of computer crime.
Phone fraud, or more generally communications fraud, is the use of telecommunications products or services with the intention of illegally acquiring money from, or failing to pay, a telecommunication company or its customers.
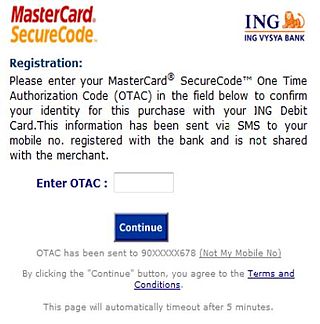
A one-time password (OTP), also known as a one-time PIN, one-time authorization code (OTAC) or dynamic password, is a password that is valid for only one login session or transaction, on a computer system or other digital device. OTPs avoid several shortcomings that are associated with traditional (static) password-based authentication; a number of implementations also incorporate two-factor authentication by ensuring that the one-time password requires access to something a person has as well as something a person knows.
A transaction authentication number (TAN) is used by some online banking services as a form of single use one-time passwords (OTPs) to authorize financial transactions. TANs are a second layer of security above and beyond the traditional single-password authentication.

Caller ID spoofing is a spoofing attack which causes the telephone network's Caller ID to indicate to the receiver of a call that the originator of the call is a station other than the true originating station. This can lead to a display showing a phone number different from that of the telephone from which the call was placed.
Voice phishing, or vishing, is the use of telephony to conduct phishing attacks.
Phone cloning is the copying of identity from one cellular device to another.
Telemarketing fraud is fraudulent selling conducted over the telephone. The term is also used for telephone fraud not involving selling.

Credit card fraud is an inclusive term for fraud committed using a payment card, such as a credit card or debit card. The purpose may be to obtain goods or services or to make payment to another account, which is controlled by a criminal. The Payment Card Industry Data Security Standard is the data security standard created to help financial institutions process card payments securely and reduce card fraud.

Multi-factor authentication is an electronic authentication method in which a user is granted access to a website or application only after successfully presenting two or more pieces of evidence to an authentication mechanism. MFA protects personal data—which may include personal identification or financial assets—from being accessed by an unauthorized third party that may have been able to discover, for example, a single password.
Cramming is a form of fraud in which small charges are added to a bill by a third party without the subscriber's consent, approval, authorization or disclosure. These may be disguised as a tax, some other common fee or a bogus service, and may be several dollars or even just a few cents. The crammer's intent is that the subscriber will overlook and ultimately pay these small charges without challenging their legitimacy or inquiring further.

"Mobile tower fraud" may be defined as a type of mass marketing fraud with advance fee fraud characteristics, where the central scheme is the installation of a mobile tower in the victim's property. The victims are lured by the promise of huge rental income. Mobile tower fraudsters are targeting individuals of all ages and demographics. With the telecommunication infrastructure booming in India to meet the socioeconomic requirements of the country, mass marketing fraudsters have seen a criminal opportunity in it.
AnyDesk is a remote desktop application distributed by AnyDesk Software GmbH. The proprietary software program provides platform-independent remote access to personal computers and other devices running the host application. It offers remote control, file transfer, and VPN functionality. AnyDesk is often used in technical support scams and other remote access scams.
Cryptocurrency and crime describe notable examples of cybercrime related to theft of cryptocurrencies and some methods or security vulnerabilities commonly exploited. Cryptojacking is a form of cybercrime specific to cryptocurrencies that have been used on websites to hijack a victim's resources and use them for hashing and mining cryptocurrency.

On July 15, 2020, between 20:00 and 22:00 UTC, 130 high-profile Twitter accounts were reportedly compromised by outside parties to promote a bitcoin scam. Twitter and other media sources confirmed that the perpetrators had gained access to Twitter's administrative tools so that they could alter the accounts themselves and post the tweets directly. They appeared to have used social engineering to gain access to the tools via Twitter employees. Three individuals were arrested by authorities on July 31, 2020, and charged with wire fraud, money laundering, identity theft, and unauthorized computer access related to the scam.

Graham Ivan Clark is an American computer hacker, cybercriminal and a convicted felon regarded as the mastermind behind the 2020 Twitter account hijacking.
The meaning of the word crypto as an abbreviation is controversial. Cryptographers - people who specialize in cryptography - have used the term "crypto" as an abbreviation for their field of study. However, "crypto" has also become a common abbreviation for cryptocurrency.
A fraud factory or fraud park is a collection of large fraud organizations usually involved in human trafficking operations, commonly found in Southeast Asia, including Cambodia, Myanmar, or Laos, and usually operated by a criminal gang. Fraud factory operators lure foreign nationals to scam hubs, where they are forced into modern slavery, to scam internet users around the world into fraudulently buying cryptocurrencies or withdrawing cash, via social media and online dating apps. Trafficking victims' passports are confiscated, and they are threatened with organ harvesting and forced prostitution if they do not scam sufficiently successfully.

Scam call centers operate in Ukraine, including major cities such as Kyiv and Dnipro. Under Article 190 of The Criminal Code of Ukraine, the activities of these call centers are considered illegal. According to Sberbank, the "capital" of phone fraud is Dnipro, and up to 95% of calls originate from Ukraine to Russians.
References
- ↑ admin (2014-05-09). "Alert – how you can be scammed by a method called SIM Splitting". Action Fraud. Retrieved 2018-08-22.
- ↑ "NPR Search : NPR". www.npr.org.
- ↑ Tims, Anna (2015-09-26). "'Sim swap' gives fraudsters access-all-areas via your mobile phone". the Guardian. Retrieved 2018-08-22.
- 1 2 "Many Bengalureans lose cash to sim card swap fraud - Times of India". The Times of India. Retrieved 2018-08-22.
- 1 2 Murphy, Margi; Bennett, Drake (August 4, 2023). "Teen Gamers Swiped $24 Million in Crypto, Then Turned on Each Other". Bloomberg Businessweek . Retrieved May 11, 2024.
- ↑ "Experts Finger Insiders in Telcos for Rising SIM Swap Fraud – Nigerian CommunicationWeek". nigeriacommunicationsweek.com.ng. 14 July 2018. Retrieved 2018-08-22.
- ↑ "You will be requested to press 1 or authenticate this Swap". Gadget Now. Retrieved 2018-08-22.
- ↑ Hartmans, Avery (12 April 2023). "A hacker ripped me off for $10,000. The scam turned out to be brilliant — and terrifying". Business Insider . Retrieved 11 May 2024.
- ↑ Franceschi-Bicchierai, Lorenzo (9 July 2020). "Verizon Adds Protection Against SIM Swapping Hacks in Mobile App". Vice . Retrieved 11 May 2024.
- ↑ Franceschi-Bicchierai, Lorenzo (2019-05-13). "AT&T Contractors and a Verizon Employee Charged With Helping SIM Swapping Criminal Ring". Vice News . Retrieved 2020-01-23.
Among the alleged criminals were also two former AT&T contract employees and one former Verizon employee, who helped the alleged criminals by providing private customer information in exchange for bribes, according to court documents.
- ↑ Franceschi-Bicchierai, Lorenzo (3 August 2018). "How Criminals Recruit Telecom Employees to Help Them Hijack SIM Cards". Vice . Retrieved 11 May 2024.
- ↑ TRUȚĂ, Filip (17 April 2024). "Scammers Are Tempting Telecom Employees with $300 Bribe Offers for SIM Swapping Help". Bitdefender . Retrieved 11 May 2024.
- ↑ Barrett, Brian. "How to Protect Your Phone Against a SIM Swap Attack". Wired– via www.wired.com.
- ↑ Brandom, Russell (August 31, 2019). "The frighteningly simple technique that hijacked Jack Dorsey's Twitter account". The Verge.
- ↑ Stempel, Jonathan (7 May 2020). "U.S. cryptocurrency investor sues suburban NYC teen for $71.4 million over alleged swindle". Reuters. Retrieved 4 January 2021.
- ↑ Nadeau, Barbie Latza (May 8, 2020) "15-Year-Old From Suburbs Led ‘Evil Computer Geniuses’ in $24M Cryptocurrency Heist: Lawsuit" Daily Beast
- 1 2 Winters, Mike (February 19, 2022). "This SIM card scam once fooled Jack Dorsey—here's how to avoid it". CNBC. Retrieved February 19, 2022.
- 1 2 Otis, Ginger Adams (February 18, 2022). "SIM-Swapping Attacks, Many Aimed at Crypto Accounts, Are on the Rise". The Wall Street Journal. Retrieved February 19, 2022.
- ↑ Kim, Myounghoon; Suh, Joon; Kwon, Hunyeong (August 2022). "A Study of the Emerging Trends in SIM Swapping Crime and Effective Countermeasures". 2022 IEEE/ACIS 7th International Conference on Big Data, Cloud Computing, and Data Science (BCD). pp. 240–245. doi:10.1109/BCD54882.2022.9900510. ISBN 978-1-6654-6582-3. S2CID 252625262.