An Internet filter is software that restricts or controls the content an Internet user is capable to access, especially when utilized to restrict material delivered over the Internet via the Web, Email, or other means. Such restrictions can be applied at various levels: a government can attempt to apply them nationwide, or they can, for example, be applied by an Internet service provider to its clients, by an employer to its personnel, by a school to its students, by a library to its visitors, by a parent to a child's computer, or by an individual user to their own computers. The motive is often to prevent access to content which the computer's owner(s) or other authorities may consider objectionable. When imposed without the consent of the user, content control can be characterised as a form of internet censorship. Some filter software includes time control functions that empowers parents to set the amount of time that child may spend accessing the Internet or playing games or other computer activities.

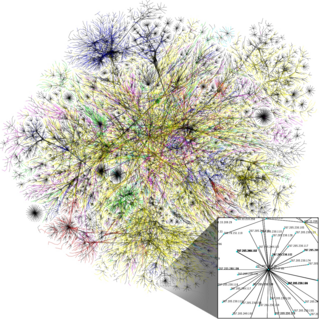
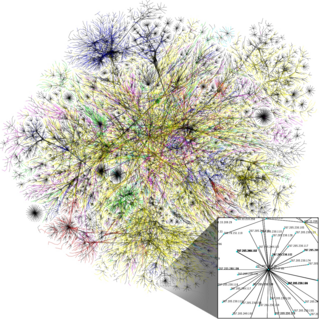
In computer networking, a proxy server is a server application that acts as an intermediary between a client requesting a resource and the server providing that resource. It improves privacy, security, and performance in the process.

Privoxy is a free non-caching web proxy with filtering capabilities for enhancing privacy, manipulating cookies and modifying web page data and HTTP headers before the page is rendered by the browser. Privoxy is a "privacy enhancing proxy", filtering web pages and removing advertisements. Privoxy can be customized by users, for both stand-alone systems and multi-user networks. Privoxy can be chained to other proxies and is frequently used in combination with Squid among others and can be used to bypass Internet censorship.
SOCKS is an Internet protocol that exchanges network packets between a client and server through a proxy server. SOCKS5 optionally provides authentication so only authorized users may access a server. Practically, a SOCKS server proxies TCP connections to an arbitrary IP address, and provides a means for UDP packets to be forwarded. A SOCKS server accepts incoming client connection on TCP port 1080, as defined in RFC 1928.
Deep packet inspection (DPI) is a type of data processing that inspects in detail the data being sent over a computer network, and may take actions such as alerting, blocking, re-routing, or logging it accordingly. Deep packet inspection is often used for baselining application behavior, analyzing network usage, troubleshooting network performance, ensuring that data is in the correct format, checking for malicious code, eavesdropping, and internet censorship, among other purposes. There are multiple headers for IP packets; network equipment only needs to use the first of these for normal operation, but use of the second header is normally considered to be shallow packet inspection despite this definition.
The Great Firewall is the combination of legislative actions and technologies enforced by the People's Republic of China to regulate the Internet domestically. Its role in internet censorship in China is to block access to selected foreign websites and to slow down cross-border internet traffic. The Great Firewall operates by checking transmission control protocol (TCP) packets for keywords or sensitive words. If the keywords or sensitive words appear in the TCP packets, access will be closed. If one link is closed, more links from the same machine will be blocked by the Great Firewall. The effect includes: limiting access to foreign information sources, blocking foreign internet tools and mobile apps, and requiring foreign companies to adapt to domestic regulations.
A dark net or darknet is an overlay network within the Internet that can only be accessed with specific software, configurations, or authorization, and often uses a unique customized communication protocol. Two typical darknet types are social networks, and anonymity proxy networks such as Tor via an anonymized series of connections.
Privacy software, also called privacy platform, is software built to protect the privacy of its users. The software typically works in conjunction with Internet usage to control or limit the amount of information made available to third parties. The software can apply encryption or filtering of various kinds.

Psiphon is a free and open-source Internet censorship circumvention tool that uses a combination of secure communication and obfuscation technologies, such as a VPN, SSH, and a Web proxy. Psiphon is a centrally managed and geographically diverse network of thousands of proxy servers, using a performance-oriented, single- and multi-hop routing architecture.
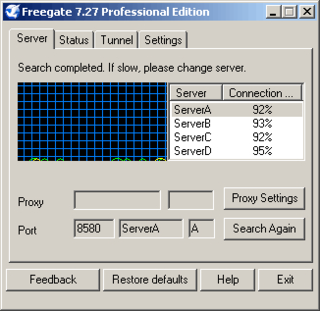
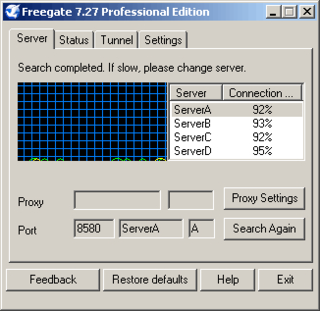
Freegate is a software application developed by Dynamic Internet Technology (DIT) that enables internet users to view websites blocked by their governments. The program takes advantage of a range of proxy servers called Dynaweb. This allows users to bypass Internet firewalls that block web sites by using DIT's Peer-to-peer (P2P)-like proxy network system. FreeGate's anti-censorship capability is further enhanced by a new, unique encryption and compression algorithm in the versions of 6.33 and above. Dynamic Internet Technology estimates Freegate had 200,000 users in 2004. The maintainer and CEO of DIT is Bill Xia.
Internet censorship is the legal control or suppression of what can be accessed, published, or viewed on the Internet. Censorship is most often applied to specific internet domains but exceptionally may extend to all Internet resources located outside the jurisdiction of the censoring state. Internet censorship may also put restrictions on what information can be made internet accessible. Organizations providing internet access – such as schools and libraries – may choose to preclude access to material that they consider undesirable, offensive, age-inappropriate or even illegal, and regard this as ethical behavior rather than censorship. Individuals and organizations may engage in self-censorship of material they publish, for moral, religious, or business reasons, to conform to societal norms, political views, due to intimidation, or out of fear of legal or other consequences.
An anonymizer or an anonymous proxy is a tool that attempts to make activity on the Internet untraceable. It is a proxy server computer that acts as an intermediary and privacy shield between a client computer and the rest of the Internet. It accesses the Internet on the user's behalf, protecting personal information of the user by hiding the client computer's identifying information such as IP addresses. Anonymous proxy is the opposite of transparent proxy, which sends user information in the connection request header. Commercial anonymous proxies are usually sold as VPN services.

Tor is a free overlay network for enabling anonymous communication. Built on free and open-source software and more than seven thousand volunteer-operated relays worldwide, users can have their Internet traffic routed via a random path through the network.
The Golden Shield Project, also named National Public Security Work Informational Project, is the Chinese nationwide network-security fundamental constructional project by the e-government of the People's Republic of China. This project includes a security management information system, a criminal information system, an exit and entry administration information system, a supervisor information system, a traffic management information system, among others.
Internet censorship circumvention, also referred to as going over the wall or scientific browsing in China, is the use of various methods and tools to bypass internet censorship.

VPN blocking is a technique used to block the encrypted protocol tunneling communications methods used by virtual private network (VPN) systems. Often used by large organizations such as national governments or corporations, it can act as a tool for computer security or Internet censorship by preventing the use of VPNs to bypass network firewall systems.
Hotspot Shield is a public VPN service operated by AnchorFree, Inc. Hotspot Shield was used to bypass government censorship during the Arab Spring protests in Egypt, Tunisia, and Libya.
uProxy was an extension for Chrome and Firefox, which allowed users to access the Internet via a web proxy. This project has been superseded by Outline VPN. The extension works by enabling a user to share their Internet connection with someone else. Google Ideas provided funding for the development which was carried out by the University of Washington and Brave New Software — the same organization behind the anti-censorship tool Lantern. The extension is intended to allow users to get more secure access to the Internet without being monitored. It is free/libre software under Apache license 2.0. The software has been discontinued, stating on their website " uProxy was an open source project led by the University of Washington and seeded by Jigsaw. Although the project is no longer supported, the code is still available on GitHub."

Lantern is a free internet censorship circumvention tool that operates in some of the most extreme censorship environments, such as China, Iran, and Russia. It uses wide variety of protocols and techniques that obfuscate network traffic and/or co-mingle traffic with protocols censors are reluctant to block. It also uses domain fronting. It is not an anonymity tool like Tor.
The Open Technology Fund (OTF) is an American nonprofit corporation that aims to support global Internet freedom technologies. Its mission is to "support open technologies and communities that increase free expression, circumvent censorship, and obstruct repressive surveillance as a way to promote human rights and open societies." As of November 2019, the Open Technology Fund became an independent nonprofit corporation and a grantee of the U.S. Agency for Global Media. Until its formation as an independent entity, it had operated as a program of Radio Free Asia.